Cybersecurity Awareness Month is an annual event that takes place every October to raise awareness about the importance of cybersecurity and promote best practices for staying safe online. This year, Cybersecurity Awareness Month 2023 marks the 20th anniversary of the event, and the theme is “Secure Our World“. The Cybersecurity and Infrastructure Security Agency (CISA) and the National Cybersecurity Alliance (NCA) are partnering to create resources and messaging for organizations to use when they talk with their employees, customers, and memberships about staying safe online.
What is cybersecurity awareness month?
Celebrated every October for the past 20 years, Cyber Awareness Month is an event about the importance of cybersecurity and promotes best practices for staying safe online.
The event was created in 2004 as a collaborative effort between the US government and industry to ensure that every American has the resources they need to stay safer and more secure online.
The Cybersecurity and Infrastructure Security Agency (CISA) and the National Cybersecurity Alliance (NCA) are partnering to create resources and messaging for organizations to use when they talk with their employees, customers, and memberships about staying safe online, such as the Cybersecurity Awareness Month toolkit.
What is the 2023 Cybersecurity Awareness Month theme?
The Secure Our World theme permeates all activities in 2023. It looks to cover the entire gamut of online cyber activities, starting with logging in and passwords. Of course, CISA recommends using strong passwords and multifactor authentication (MFA), something the agency has been promoting for years. But the Secure Our World theme goes beyond that, encouraging everyone to take steps each day to protect themselves when online or using connected devices. That is because national cyber security awareness doesn’t end in October.
The Cybersecurity Awareness Month 2023 toolkit provided by CISA is an essential resource for organizations to promote cybersecurity awareness in their workplace. The toolkit includes a guide for creating a cybersecurity awareness program, social media graphics, and other resources to help organizations promote cybersecurity awareness.
The Importance of Cybersecurity Awareness Month
The Cybersecurity Awareness Month is an important initiative that aims to raise awareness about digital security and empower everyone to protect their personal data from cybercrime.
Cybersecurity threats are becoming more sophisticated and frequent. Cybercriminals during ransomware attacks not only encrypt data but also exfiltrate sensitive data and threaten to publish or sell these data online if a ransom is not paid. And other types of cyber attacks, like DDoS attacks, threaten companies and organizations by denying access to critical data or preventing users from accessing online information.
Therefore, organizations of all sizes and industries must create and implement strategies to protect their sensitive data and systems from cyber threats.
The goal of Cybersecurity Awareness Month is to provide an opportunity to educate individuals and organizations about the importance of cybersecurity and promote best practices for staying safe online every day.
Tips for celebrating Cybersecurity Awareness Month
The best way to celebrate Cybersecurity Awareness Month in 2023 is by following its theme and applying solutions towards securing businesses and individual data.
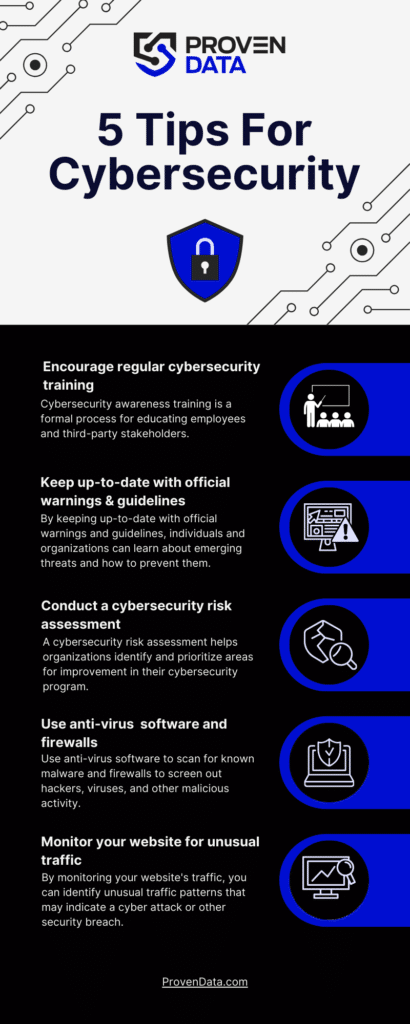
Conduct cybersecurity awareness training
Cybersecurity awareness training is a formal process for educating employees and third-party stakeholders, like contractors and business partners, on how to protect themselves and their organizations from cyber threats. It is an essential part of any organization’s cybersecurity strategy and helps minimize the risk of cyberattacks and other security breaches.
Keep up-to-date with official warnings & guidelines
Multiple reputable organizations are focused on stopping cyber criminals and reducing the damage they can cause. By keeping up-to-date with official warnings and guidelines, both individuals and organizations can stay informed about the latest cybersecurity threats and best practices, which improves their network security.
1. Follow official advisories and guidelines
Official sources that work with government and private sector partners to implement cyber security policies regularly update their data on new cyber threats daily. The Cybersecurity and Infrastructure Security Agency (CISA) and the National Security Agency (NSA) are priceless resources for thorough advisories and guidelines.
As for making sure your data security efforts are up-to-par, The Federal Trade Commission (FTC) and the National Institute of Standards and Technology (NIST) guidelines also can help businesses stay aware of how to apply data security demands to their specific industries.
2. Stay informed about cybersecurity news
News media and cybersecurity publications have been closely following the worrying increase in cyber attacks and can help you stay informed about cybersecurity news and trends.
3. Attend cybersecurity events
Conferences and webinars on cybersecurity and data protection are essential to learn about the latest cybersecurity threats and best practices to prevent them.
Conduct a cybersecurity risk assessment
A cybersecurity risk assessment evaluates an organization’s ability to protect its information from cyber threats. It helps organizations identify and prioritize areas for improvement in their cybersecurity program and communicate their risks to stakeholders.
Organizations can conduct cybersecurity risk and vulnerability assessments with internal resources or with external assistance, such as with Proven Data’s cyber security services.
A 6-step cybersecurity risk assessment checklist:
1. Audit of assets
Identify all information assets that could be affected by a cyber attack, such as hardware, systems, laptops, customer data, and intellectual property.
2. Identify potential consequences
Learn about various risks that could affect those assets, such as malware, phishing, social engineering, and insider threats.
3. Identify threat sources and threat events
A forensic report can identify the sources of the threats and the events that could lead to a cyber attack.
4. Identify existing security controls
Check whether existing security controls are in place to protect against cyber threats.
5. Assess risk and probability impact
Classify potential risks in a logical formula and assign a value of “high”, “moderate”, or “low”.
6. Develop a risk management plan
Your risk management plan must include recommendations for mitigating in case of an attack and should prioritize the implementation of security controls.
Boost your systems and network security
To boost your network security you can use anti-virus software to scan for known malware and firewalls to screen out hackers, viruses, and other malicious activity.
You must also implement network segmentation, so each employee has access only to the data they need to perform their tasks. Plus, ensure you’re using methods that enable endpoint security.
How can antivirus software help with cybersecurity
Anti-virus software is designed to detect and remove malware from computers and networks. It scans files and software running on a host or server and compares them to a database of known malware. If it finds a match, then the anti-virus may quarantine or delete the malware based on the endpoint security policy.
How can firewalls help with cybersecurity
Firewalls are network security devices that prevent unauthorized access to a network. They inspect incoming and outgoing traffic using a set of security rules and parameters that can be pre-set within the platform. Any data packets that violate the rules set within the firewall software are filtered out and denied access to the network, protecting against potential threats.
How can network segmentation help with cybersecurity
Network segmentation is a strategy used to segregate and isolate segments in the enterprise network to reduce the attack surface. It limits users’ access privileges to only those who need them and improves access control for external and internal network security.
Monitor your website for unusual traffic
By monitoring your website’s traffic, you can identify unusual traffic patterns that may indicate a cyber attack or other security breaches. Use a web traffic monitoring tool to collect, analyze, and categorize your network’s flow data into readable graphs, tables, and reports. You must also look for unusual traffic patterns, such as spikes in traffic or traffic from unusual locations or IP addresses or bot traffic, which can be created by malicious actors with the intention of manipulating website data or disrupting normal user activity.
Set up alerts to notify you when unusual traffic patterns are detected and regularly review traffic logs to identify any unusual activity that may have gone undetected by automated monitoring tools.
4 simple methods to strengthen your cybersecurity today
Cybersecurity can get complex, but there are simpler methods you can apply to your systems today that will go a long way to making yourself and your business safer from cyber threats. It starts with promoting the 4 simple steps to stay safe online, which include securing your devices, protecting your personal information, connecting with care, and being cyber-aware.
Let’s break down those steps into 4 methods you can apply today:
1. Implement multi-factor authentication (MFA)
Applying MFA to all of your accounts makes it significantly less likely for hackers to gain access to your sensitive information.
2. Regularly update software
Every software, program, and app you use on your devices must be regularly updated. Including browsers, operating systems, and applications, to ensure that they are protected against known vulnerabilities.
3. Implement user privilege and network segmentation
User privilege limits user access to only the resources they need to perform their job functions. Network segmentation divides a network into smaller segments, each with its own security controls and access permissions. Both solutions help to reduce the risk of insider threats and limit the damage that can be done if a user account is compromised.
4. Ensure your privacy online
Protect your personal information by using strong passwords, avoiding public Wi-Fi, and being cautious of what you share online. You can use apps and security software, such as antivirus and VPN, to help protect your personal information and keep your privacy online.
Plus, be cautious of unsolicited emails, texts, and phone calls, and avoid clicking on links or downloading attachments from unknown sources. If you receive a suspicious email, report it to your IT department or delete it.