Cybersecurity experts since 2011.
From a data recovery lab to a full-spectrum cybersecurity firm, Proven Data has spent over a decade helping organizations respond to, recover from, and prevent cyber incidents.
14+
Years in Operation
3,000+
Incidents Resolved
80%
Resolved Without Ransom
4.9/5
Trustpilot Rating
Our Journey
A decade of building trust.
Founded as Data Recovery Lab
Proven Data launched as a specialized data recovery firm, developing proprietary techniques to recover data from damaged storage media and emerging ransomware variants.
Ransomware Recovery Pioneer
Became one of the first firms to systematically reverse-engineer ransomware encryption, achieving data recovery without ransom payments in a majority of cases.
Full IR & Forensics Expansion
Expanded into full incident response, digital forensics, and cyber settlement services. Launched 24/7 emergency response operations and OFAC-compliant negotiation capabilities.
Porthas Acquisition & Lynx Platform
Acquired by Porthas and launched the Lynx platform — an integrated cybersecurity SaaS bringing case management, threat intelligence, and forensic tooling under one roof.
What Drives Us
Our core values.
Team Excellence
Our people are our greatest asset. We invest in continuous training and certifications to maintain an elite team of cybersecurity professionals.
Recovery-First Approach
We exhaust every technical avenue to recover data without paying ransoms. Our R&D lab constantly develops new decryption techniques.
Rapid Response
When an incident strikes, minutes matter. Our 24/7 team mobilizes immediately with a proven process honed across thousands of engagements.
Forensic Rigor
Every investigation follows forensically sound methodologies. Our findings are court-admissible and meet the standards of insurance carriers and regulators.
Client Partnership
We treat every engagement as a partnership. Transparent communication, clear timelines, and no surprises — from first call to final report.
Leadership
Meet the team leading the charge.

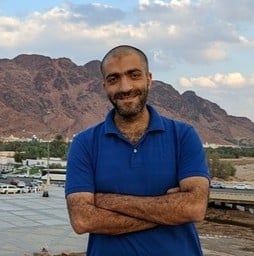
Director of Operations
George oversees the day-to-day operations of Proven Data, ensuring that every client engagement runs smoothly from intake to resolution. He has built and scaled the operational processes that allow the team to handle a high volume of concurrent cases without compromising quality.
The Team
The people behind every recovery.
Ready to talk? Reach out today.
Whether you need incident response, want to strengthen your security posture, or are evaluating partners — our team is here to help.
1 (877) 364-5161