The U.S. Federal Bureau of Investigation (FBI) and the Department of Justice (DOJ) recently announced a transformation within their efforts to stop ransomware.
According to the Wall Street Journal, FBI Director Christopher Wray compared the shift in ransomware defenses to the U.S’s fight against terrorism after 9-11.

In his first public comments following the recent ransomware attacks on critical U.S. supply chains, Wray paralleled the level of priority, disruption tactics, and prevention methods to that of the government’s 9-11 response.
Wray also emphasized the collaboration necessary to stop cyber crime.
By the end of this article, you will:
- Understand why the FBI, DOJ shift is important to national security
- Learn how you can do your part to stop ransomware under this new precedent
- Be ready to start proactively protecting your organization from ransomware
What does the new FBI, DOJ prioritization of ransomware mean?
Senior White House officials have characterized ransomware as an urgent national-security threat and report that they are currently pursuing ways to interrupt the cyber criminal system responsible for the recent spate of attacks.
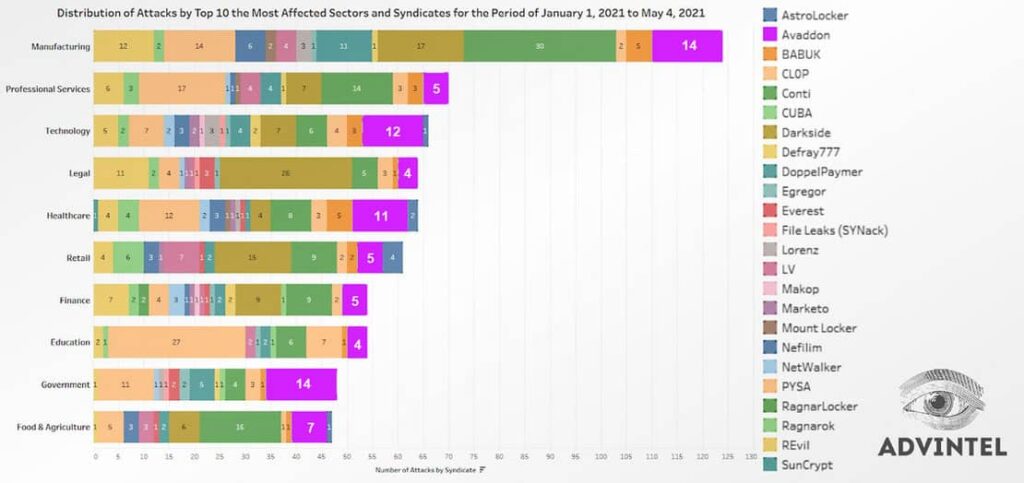
The FBI is currently investigating 100 different ransomware variants that have been traced to recent attacks.
Wray’s parallels between recent ransomware attacks and the 9-11 terrorist attack convey an assumed belief ransomware has the potential to do more than shut down critical supply chains and affect the U.S. economy; ransomware can cause life-threatening disruptions.
Wray underlined the importance of everyone doing their part to improve cyber security, commenting on the need for “shared responsibility, not just across government agencies but across the private sector and even the average American.”
Acting Director of the Cybersecurity and Infrastructure Security Agency (CISA), Brandon Wales, expressed the need for more collaboration to fight cyber crime as well, stating that government, law enforcement and the private sector improve their efforts to fight ransomware crime.
“We want to make the U.S. law enforcement community have better ability to go after, find them, track the money and get it back,” Wales said. “We recognize that the U.S. government needs to do more and [the] private sector needs to do more.”
Reporting a ransomware attack is the first step to help provide law enforcement agencies with the information they need to bring cyber criminals to justice.
How can I participate in this effort to stop ransomware?
Regardless of the size of your organization, ransom amount requested, the extent of the damage or the chosen method of ransomware recovery, you should always report a ransomware attack to law enforcement.
Collaboration efforts have already begun with internal guidance sent to U.S. attorney’s offices across the nation. This guidance contained information about the central coordination of ransomware investigations.
DOJ principal associate deputy attorney general, John Carlin, explained how the guidance details a “specialized process to ensure we track all ransomware cases regardless of where it may be referred in this country, so you can make the connections between actors and work your way up to disrupt the whole chain,” Carlin said.
Investigations are to be conducted alongside the new ransomware task force. The Ransomware and Digital Extortion Task Force is already responsible for the retrieval of a portion of the Colonial Pipeline ransom, the first operation of this kind.
In a prepared testimony, Colonial CEO Joseph Blount directly credited collaboration with the government to the success of their recovery, stating, “our engagement with those Federal authorities helped us achieve meaningful milestones in our response process to address the attack and restore pipeline operations as quickly as possible.”
The FBI has requested a $40 million new budget designated for cyber investigations and support 155 new positions.
In an FBI budget hearing on June 23, Wray discussed the need for transparency and collaboration between ransomware victims and the FBI, telling senate appropriators “most important thing is that [ransomware victims] reach out and connect…with us as quickly and transparently as possible.”
Wray added that while he hasn’t endorsed specific policy proposals yet, private sector collaboration with the FBI is critical and “anything that helps provide more incentive for that to happen, I think is a step in the right direction,” Wray said.
The shift towards ransomware prevention is vital. Via threat intelligence and information sharing between private sector and governmental agencies, action can be taken to strengthen ransomware defenses across the nation.
Deputy Assistant Director FBI Cyber Division Tonya Ugoretz acknowledged the necessity of governmental and private sector collaboration, stating “the private sector holds valuable cyber threat intelligence that exists nowhere else.”
Don’t want to be a ransomware victim?
Talk to one of our cyber security experts to discuss the needs of your organization.
Request a cyber security consultation
Reduce your risk of ransomware today
Ransomware is a matter of when, not if. Creating and continually updating your ransomware incident response plan is critical.
Protecting your organization with proactive cyber security practices will reduce your risk of becoming a victim of ransomware.
Attacks on small and medium-sized businesses may not make the headlines like critical infrastructure and government agencies, but smaller organizations are equally responsible for ensuring the security of the future.
At Proven Data, we are committed to helping organizations navigate ransomware attacks and recover their data as quickly as possible. Additionally, we want to help you safeguard data and devices to prevent ransomware attacks (we even produced a documentary about it with Fmr. FBI Special Agent Patrick Gray of the Computer Crimes Squad).
If you are a victim of a ransomware attack or would like to learn more about implementing proactive cyber security at your organization, reach out to our cyber security experts to get started.