In recent cybersecurity landscapes, ESXi ransomware has emerged as a new and potent strain of ransomware. This malware poses a significant risk to virtualized environments, particularly those leveraging VMware ESXi hypervisors.
In this article, we explore the intricacies of ESXi ransomware, like its characteristics, identification methods, operational details, and notable attacks. Plus, we offer tips on how to prevent ransomware attacks on your systems and network.
Decryptor: The Cybersecurity and Infrastructure Security Agency (CISA) has released a recovery script to aid organizations impacted by ESXiArgs ransomware attacks.
ESXi ransomware overview
The ESXi ransomware has specifically targeted VMware’s ESXi servers, which form the backbone of virtualized environments in numerous enterprises.
This malicious software leverages vulnerabilities, with a notable example being CVE-2021-21972, a critical flaw residing in the vCenter Server. Exploiting such weaknesses grants unauthorized access, enabling threat actors to execute remote code on ESXi servers.
A distinctive characteristic of this ransomware lies in its incremental encryption approach. It selectively encrypts specific file types associated with virtual machines, strategically leaving chunks of data unencrypted within large files.
The ESXi ransomware has showcased a global impact, affecting organizations across diverse regions. Beyond technical disruptions, its consequences extend to potential financial losses and reputational damage.
How to identify ESXi ransomware: Main IOCs
Indicators of compromise (IOCs) are pieces of forensic data that can help identify malicious activity or malware associated with a cyber attack. It includes the encryption extension, file hashes, and IP addresses, among other details cyber criminals leave as they infect a machine or system.
But, if you can’t identify the ransomware strain through its IOCs, you can use Proven Data’s free ransomware ID tool to check if the ESXi ransomware is the malware that encrypts your files.
Important: Some of these indicators require technical knowledge of the infected system, so you may need to contact your IT team or a digital forensics service provider.
ESXi-specific IOCs include:
Unusual Network Activity. Unusual traffic, particularly on port 427 (OpenSLP port), may indicate potential ESXi ransomware activity.
Creation of Encrypted Files. Detection of new or modified encrypted files on the ESXi server, which may have extensions appended or altered.
Abnormal System Behavior. Detection of abnormal system behavior, including unexpected file deletions, replacements of system files (e.g., index.html and motd), and alterations to VM configurations.
How ESXi ransomware works
The ESXi ransomware attack methodology involves a systematic process employed by threat actors to compromise VMware’s ESXi servers and demand ransom for the restoration of encrypted data.
Here is a breakdown of the key steps involved in the ESXi ransomware attack:
Initial access
The attackers identify and target VMware’s ESXi servers’ vulnerabilities. These vulnerabilities provide an entry point for threat actors to execute remote code on the compromised servers.
In this case, the CVE-2021-21972, a critical flaw in the vCenter Server, is exploited to gain unauthorized access to ESXi servers.
File encryption
ESXi ransomware adopts an incremental file encryption strategy. This is a strategy employed by ransomware to selectively encrypt specific files or portions of data rather than encrypting the entire content of a target system.
In the context of the ESXi ransomware attack, the incremental file encryption strategy involves encrypting specific file types associated with virtual machines, leaving chunks of data unencrypted within large files.
Specific file types associated with virtual machines, including
- .vmdk
- .vmx
- .vmxf
- .vmsd
- .vmsn
- .vswp
- .vmss
- .nvram
- .vmem
Ransom demands
After encrypting the data, the attackers issue ransom demands to the compromised organizations. These demands typically involve payments in cryptocurrencies, such as Bitcoin, in exchange for providing decryption keys.
Important: Do not pay the ransom. Paying the ransom does not guarantee that you will get your data back, and it may encourage the attackers to continue their criminal activities. Check our in-depth article on what happens if you pay the ransom.
How to handle an ESXi ransomware attack
It is important to note that handling a ransomware attack can be complex and requires expertise. Therefore, it is recommended to seek professional help from a reputable data recovery service, such as Proven Data to help you recover your data and remove the ransomware from your system.
You can also report the attack to law enforcement agencies, such as the FBI, and cybersecurity organizations to help prevent future attacks and catch the perpetrators.
We strongly recommend contacting cybersecurity services to handle ransomware attacks. Proven Data technicians not only retrieve ransomware-encrypted data but also create forensic reports and streamline incident response, minimizing your business downtime and financial loss.
How to prevent ransomware attacks
Preventing ESXi ransomware attacks is always the best cybersecurity tactic. If you are a recent victim, you must follow these tips to avoid a new ransomware attack:
Keep your software up to date
Regularly update your operating system and programs to uphold security standards. Reputable OS providers will consistently check their software for vulnerabilities and patch up their security standards to protect against newly detected threats.
Use reputable antivirus software
Employ reputable antivirus software to bolster protection against malware significantly, and regularly check that it is updated. You can also check your network for vulnerabilities and learn where you need to improve your security system.
Be cautious of suspicious emails
Even though there are no known cases of ESXi ransomware using phishing as an attack method, it’s important to exercise caution when dealing with emails from unfamiliar or dubious origins. Refrain from opening files or clicking on links within emails that you are not expecting or seem suspicious.
Do not download cracked software
Cracked software is the term used to describe illicitly modified or pirated versions of commercial software, typically distributed without proper authorization or licensing. Cybercriminals frequently conceal their ransomware executables within cracked software distribution websites, leading users to unwittingly download and execute the malware.
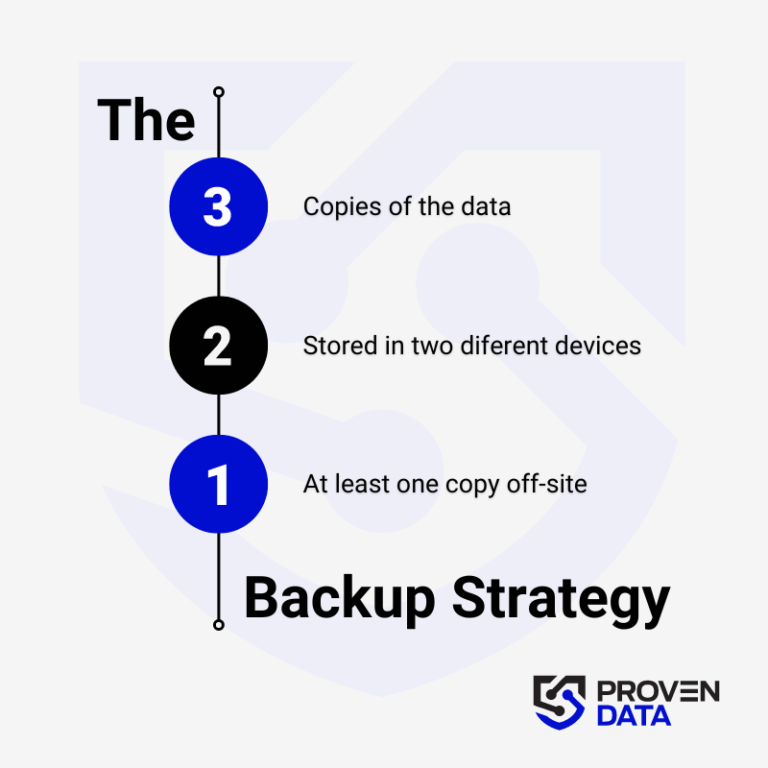
Backup your data
Regularly back up your data to an external hard drive or cloud storage service to prevent complete data loss in case of a ransomware attack. A highly recommended strategy for data loss prevention is the 3-2-1 backup strategy.
The 3-2-1 backup strategy involves creating three total copies of your data: two on different media and one offsite, ensuring redundancy and protection against data loss. And at least one copy offsite to prevent loss due to natural disasters or other local incidents.
Educate yourself and your teams
Educate yourself and your employees about the risks of ransomware and how to avoid it, such as avoiding suspicious emails or downloads.
Consult cybersecurity professionals
Proven Data offers cyber security services to help you keep your data protected against threat actors. From vulnerability assessment to ensure your systems and servers do not have open doors for cyber attacks, to Incident Response (IR) services for immediate response in case of a successful attack.
We also have the option of managed detection and response (MDR) services that help organizations improve their security posture, minimize risk, and protect sensitive data and assets.