The digital age has brought unprecedented opportunities for businesses, but it has also ushered in an era of escalating cybercrime. It’s no longer a question of if a business will be targeted but when.
This relentless threat translates into staggering financial losses, as evidenced by the fact that the theft of digital information has become the most commonly reported fraud, surpassing physical theft. The theft of digital information has become the most commonly reported fraud, surpassing physical theft. In 2023, cyber crimes cost U.S. businesses and organizations $10 billion, a significant increase from the previous year’s $6.7 billion. Globally, experts predict that the estimated cost of cybercrime will rise from $8.44 trillion in 2022 to $23.84 trillion by 2027.
Increased online services, more sophisticated attacker tactics, and a lack of cybersecurity awareness and skills are factors driving cybercrime. For this reason, individuals and businesses should adhere to fundamental cybersecurity best practices, making it harder for threat actors to access personal information.
What is cybersecurity?
Cybersecurity is the practice of protecting computer systems, networks, and digital information from theft, damage, unauthorized access, or any form of cyberattack. The objective is to ensure information confidentiality, integrity, availability, and computer systems and data security.
The importance of cybersecurity extends beyond individual protection. It safeguards sensitive data, privacy, and technological infrastructure from diverse threats like hackers, malware, ransomware, and phishing.
For businesses, applying cybersecurity best practices not only reduces the risk of cyberattacks but also enhances customer trust, ensures business continuity, and fosters legal compliance, contributing to a proactive and responsible business image.
Cybersecurity best practices
Cybersecurity solutions must evolve to ensure data privacy as cyber threats become more robust. By consistently implementing these best practices, individuals and organizations can significantly reduce their risk of being cyber-attack victims and contribute to a safer digital environment.
1. Promote cyber hygiene
Cyber hygiene involves cultivating good digital habits and educating users about basic security practices, such as updating software, avoiding suspicious links, and using strong passwords.
Train employees in security principles
Establish basic security practices and policies for employees, such as requiring strong passwords, and establish appropriate Internet use guidelines that detail penalties for violating company cybersecurity policies. Establish rules of behavior describing how to handle and protect customer information and other vital data. Additionally, conduct periodic cybersecurity awareness training to reinforce these principles and educate employees about emerging threats.
Regularly update and patch software
Keeping software updated is crucial for addressing vulnerabilities and strengthening security. Regular patches and updates provided by software vendors help mitigate the risk of exploitation by ensuring that systems have the latest security features.
Use strong and unique passwords
Strong and unique passwords are a fundamental defense against unauthorized access. Encouraging the use of complex passwords, avoiding easily guessable combinations, and utilizing password management tools also enhance security.
2. Conduct periodic security audits
Periodic security audits are essential for evaluating the effectiveness of cybersecurity measures. Organizations can identify and address potential risks by regularly assessing vulnerabilities, strengths, and weaknesses in systems, ensuring a robust and up-to-date security posture.
You can contact a cybersecurity consulting service to help ensure your systems do not have vulnerabilities that threat actors can exploit. These professionals can also combine technology and human expertise to detect, respond, and remedy threats.
3. Segment network access
Network segmentation involves dividing a network into isolated segments to contain potential breaches. By restricting access based on roles and responsibilities, organizations minimize the impact of security incidents and enhance overall network security.
4. Implement zero-trust security
Zero-trust security verifies every user and device, regardless of their location within or outside the network. This approach minimizes the risk of unauthorized access and lateral movement within the network.
5. Ensure endpoint protection
Endpoint protection safeguards individual devices (endpoints) from cyber threats. Employing antivirus software, firewalls, and other security measures on each device ensures a comprehensive defense against malware, ransomware, and other malicious activities.
6. Enable multi-factor authentication (MFA)
Multi-factor authentication adds an extra layer of security by requiring users to provide multiple forms of identification before accessing an account or system. This significantly reduces the risk of unauthorized access, even if passwords are compromised.
7. Secure remote desktop protocol (RDP)
Securing Remote Desktop Protocol involves implementing measures to protect remote access to systems. This includes using strong encryption, enabling network-level authentication, and restricting RDP access to authorized users.
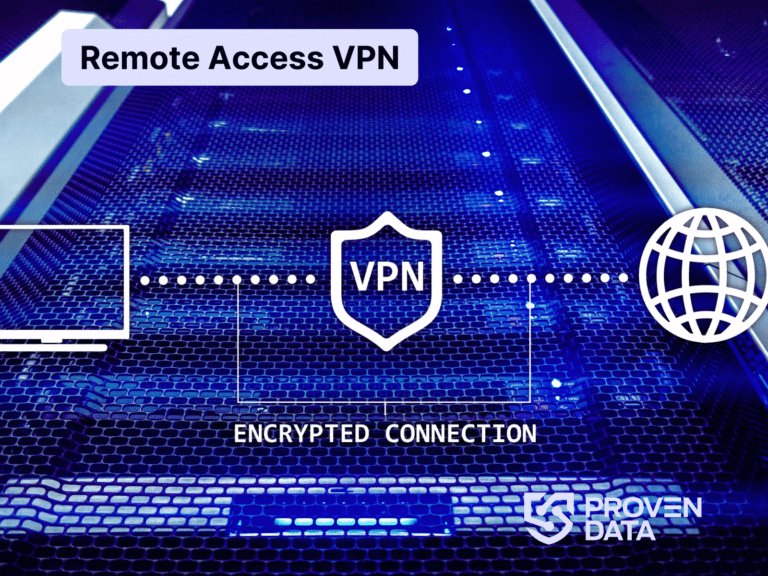
8. Use a virtual private network (VPN)
A Virtual Private Network (VPN) enhances online privacy and security by encrypting internet connections. It protects data from interception, especially when using public Wi-Fi networks. VPNs create a secure tunnel for data transmission, shielding users from potential cyber threats.
9. Stay informed about cyber threats
10. Regularly back up your data
Regular data backups are a key recovery strategy in the event of data loss or a security incident. By storing copies of important files in secure locations, organizations can quickly restore data and minimize disruptions caused by cyberattacks or other unforeseen events.
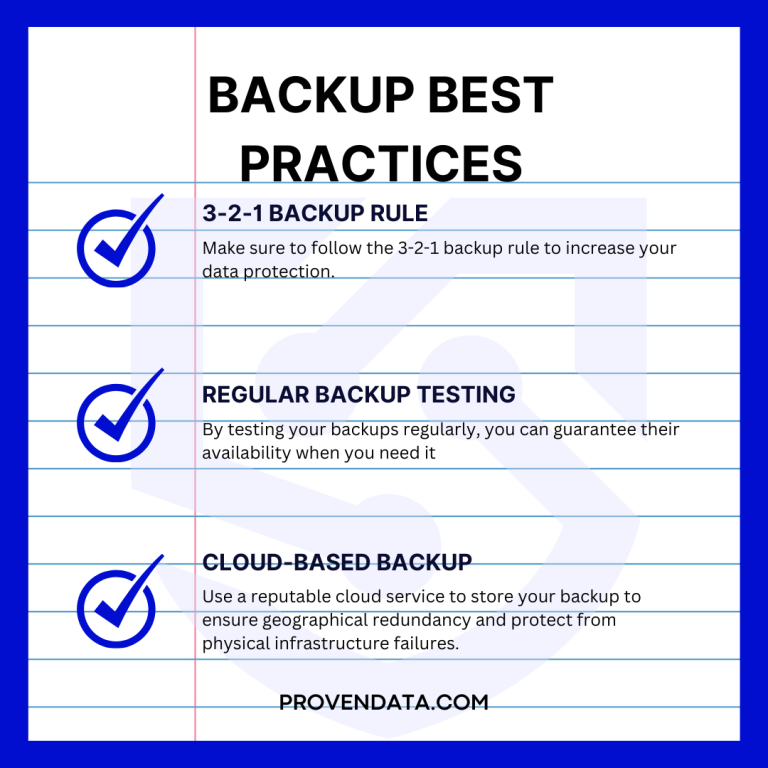
The 3-2-1 backup strategy is the most recommended backup method to ensure data security since this strategy provides a comprehensive and resilient approach to data protection, minimizing the risk of data loss and enhancing the chances of successful recovery in various scenarios.
11. Provide firewall security for your Internet connection
A firewall is a set of related programs that prevent outsiders from accessing data on a private network. Ensure the operating system’s firewall is enabled or install free online software. If employees work from home, ensure that a firewall protects their home system(s).
12. Create a mobile device action plan
Mobile devices can create significant security and management challenges, especially if they hold confidential information or can access the corporate network. Require users to password-protect their devices, encrypt their data, and install security apps to prevent criminals from stealing information while the phone is on public networks. Be sure to set reporting procedures for lost or stolen equipment.
How the Proven Data cybersecurity team can help
Proven Data’s dedicated team of experts is committed to guiding you through the intricate realm of IT, offering customized solutions aligned with your business requirements. Our incident response services are crafted to respond promptly to security breaches, minimizing both damage and downtime.