The housing industry recently fell prey to a sophisticated and crippling cyber assault. The target, a company whose exact size and identity must remain confidential, experienced a malicious ransomware attack. The company’s critical data, primarily associated with fraud and phishing, was encrypted, effectively halting routine
Hours for complete data recovery
Ransom demanded
Total recovery service cost
Incident
The ransom demand was a staggering $700,000. The cybercriminals behind the attack demonstrated their control and issued this demand in a chilling, anonymous message. The company had to react swiftly when faced with the potential loss of sensitive data and devastating operational downtime.
Response
The immediate course of action was to engage the services of our team at Proven Data. Our expertise in digital forensics was put to the test in this mission-critical scenario. Negotiating the ransom was an option on the table and, through careful and strategic discussions, we managed to reduce the demand to $150,000.
Recovery
Our response was rapid and effective. In less than 24 hours, entire operations were restored. Our digital forensics study played a crucial role in the recovery process. We used cutting-edge techniques to decrypt the data and regain control. The speed of the recovery process minimized the potential damage, both financial and reputational, for the company.

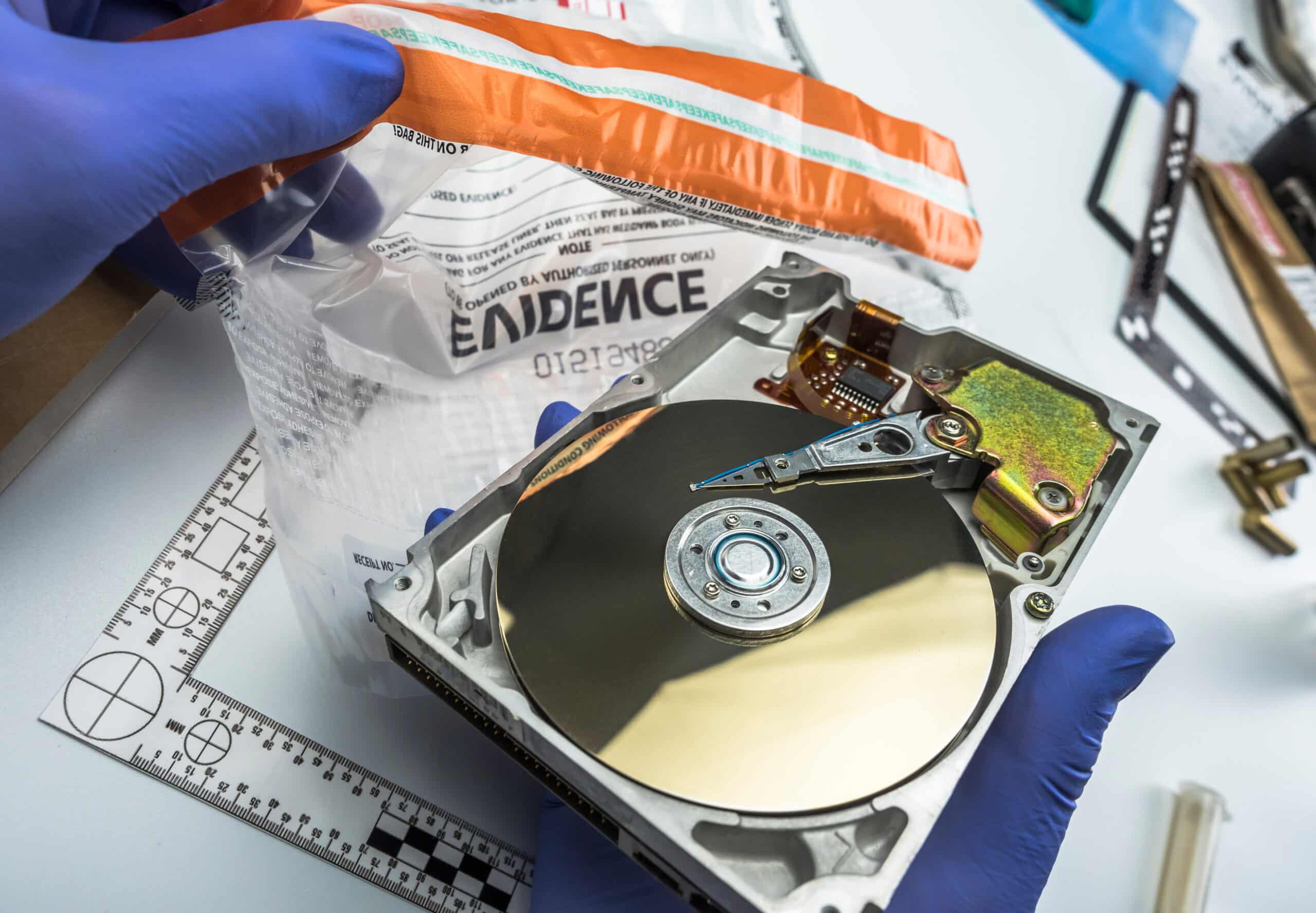
Proven Data's Digital Forensics Analysis
We first assessed the extent of the breach and the type of ransomware involved. This step allowed us to understand the complexity of the attack and strategize our response.
Our team, experienced in dealing with such scenarios, took charge of the ransom negotiations. We managed to reduce the ransom demand from $700,000 to $150,000.
Utilizing advanced digital forensics techniques, we began the process of decrypting the encrypted data. This step required a delicate approach to avoid any further damage to the data.
After decryption, we restored the company’s systems back to full functionality. The entire recovery process was completed in less than 24 hours, minimizing operational downtime.
To prevent future attacks, we conducted a thorough post-recovery analysis. This involved identifying the security loopholes that allowed the breach and recommending measures to fortify the system.
We prepared a detailed forensic report, outlining the incident and our response. This was submitted to the company for future reference.
The Results
- Complete Data Decryption
- Data Recovery
- Data De-Corruption
- Disaster Mitigation
- Ransomware Prevention Assistance
- Ransom Cost Reduction

